
Hey there! Before we jump into the details, Just to clarify a few things: 1) I hack ethically. No personal gains. Although, I believe hackers should be positively awarded for their contributions. 2) The reason why I’m writing this article today is to inform more people about the possible security lapses & encourage Indian firms to opt for bug bounty programmes to counter the same. Until now, I’ve hacked into a dozen Indian companies. Mostly all within a month last year. It’s a big deal, right? A 20-something guy with no professional expertise, just a passion to hunt gold, can be such a big pain for the corporates. Not trying to brag here. Just portraying the current security scenario in the country. I wouldn’t say I stumbled upon their API’s accidentally while working on a weekend project or something. I deliberately tried to hack into each one of them. This is just something I love. Obviously, I never shared any of my findings with anyone else. I’m doing it now because their applications have been updated & the bugs have been removed.
Air India I reached out to the CEO of Air India through e-mail on 4th November, 2015.
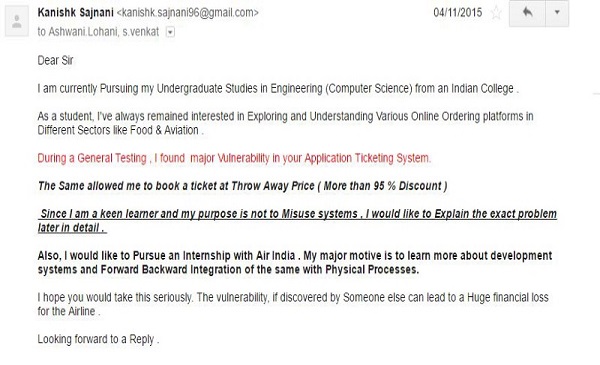
Following the email, I received an unexpected phone call from their Manager (Finance) on 12th Nov, 2015. He asked me to prove if such a vulnerability existed & Oh boy! Did I?
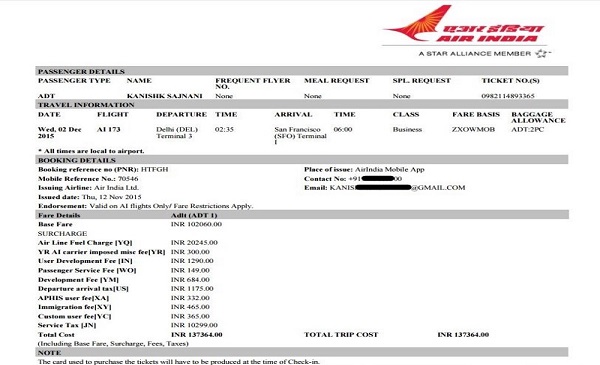
This was a legitimate PNR generated airline ticket. I could have traveled to the States for absolutely free. Odds are they would have never even found out I did. The Manager further enquired about the rectification steps required. I sent him all the details along with POC( Proof of Concept ) videos attached in mail. He also told me that they had their own IT team. I was keen on doing an internship back then. He kindly accepted my request( I never actually interned though) & also thanked me heartily for the contribution I had made.
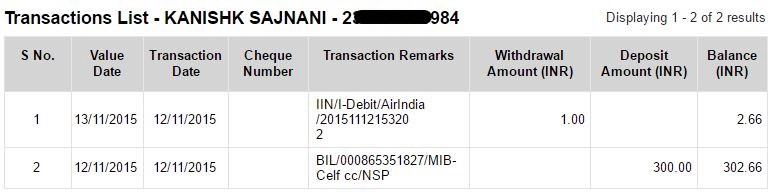
SpiceJet Now, this was one of the most bizarre experiences I ever had. Just like Air India, I had found a similar vulnerability in SpiceJet’s Mobile application too.

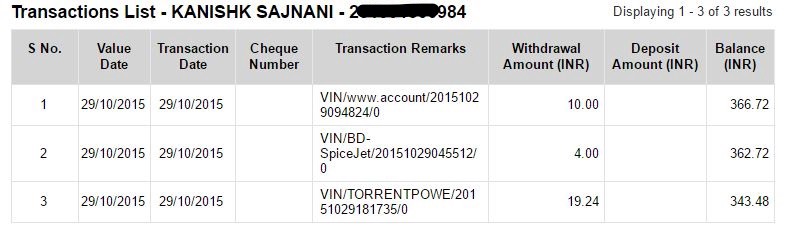
The above ticket was booked on 28th October. Travel date was exactly a month after. I was hoping that the transaction would eventually get flagged & somebody from the Head Office would contact me. To my surprise, that never happened. I decided to drop a mail to some senior official. Shockingly, I wasn’t even able to find out the email addresses of their CEO or CTO or CMO. All I could manage to find were these ( custrelations-nodalofficer & apppelateauthority@spicejet.com) With no other choice left, I sent a similar email ( like one to Air India) to SpiceJet too. Their reply baffled me.
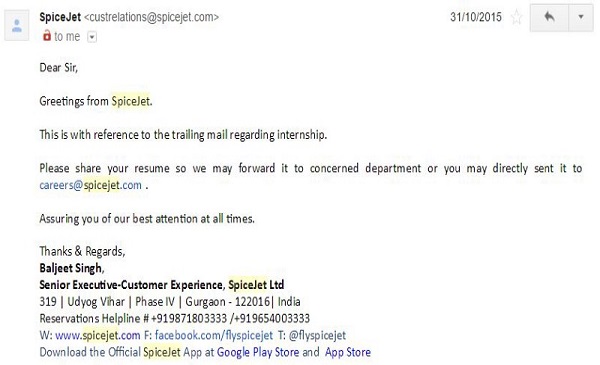
I had to find an alternative, obviously. I tried reaching out to Mr Pradeep Shah (GM, Reservations). As requested, I forwarded him the same e-mail I had sent to SpiceJet earlier. What followed was something I never expected. They sent me our previous correspondence in a .eml type file attached. This time the mail was signed by their Nodal Officer. Either they didn’t understand the point I made or they didn’t like to acknowledge the fact that their security was compromised. The ticket was absolutely valid until I decided to cancel it myself on 21st November. The cancellation mail didn’t mention any refund amount. Out of curiosity, I called their Helpline. The representative on phone told me that I was eligible for a refund of around Rs 2,000 & I can either choose to credit that amount in my debit card or use it for my next trip. Easy money, right? I could have not only traveled for free but also made money hand over fist. The financial systems in the back-end were obviously not able to detect any payment irregularities. Despite everything that happened, I decided to stay mum & leave them on God’s good grace.
Cleartrip With Cleartrip, I could have booked Flights, Hotels, International holidays, Trains, Restaurant dates, Massages, Cultural events, Sport Activities, Anything for Absolutely free.
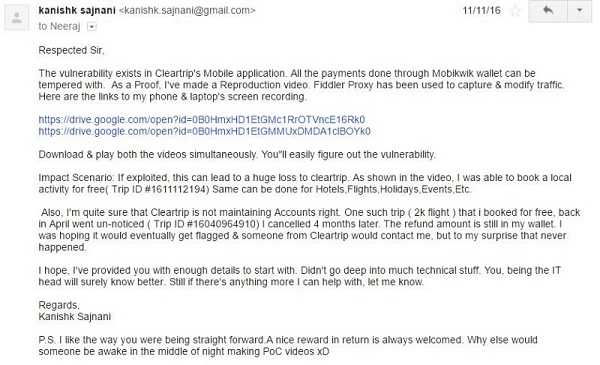
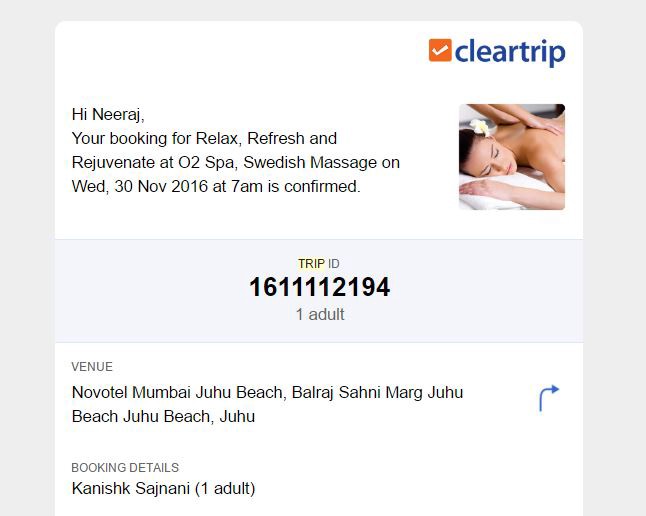
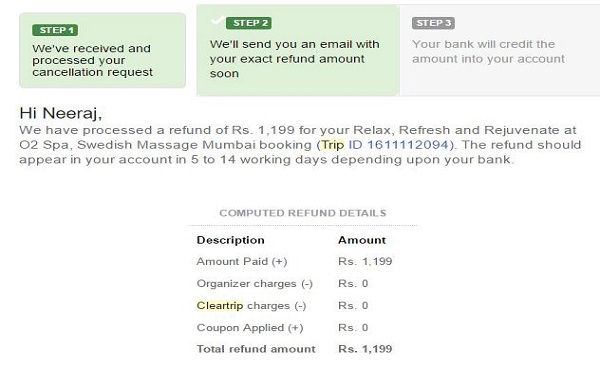
The day I made their POC videos, I had a couple of failed transactions too. One of them was automatically processed as ‘ Money Paid but failed’. A refund request was generated. My Mobikwik wallet was credited with 1199 Rupees.
Interestingly, that was the last time I ever heard from him. Mobikwik wallet was soon taken down from their application & never put back up. I was under the impression that maybe they were updating the API’s. A month later, I finally emailed him back. Got nothing in return. Frustrated, I decided to write back to the co-founders.
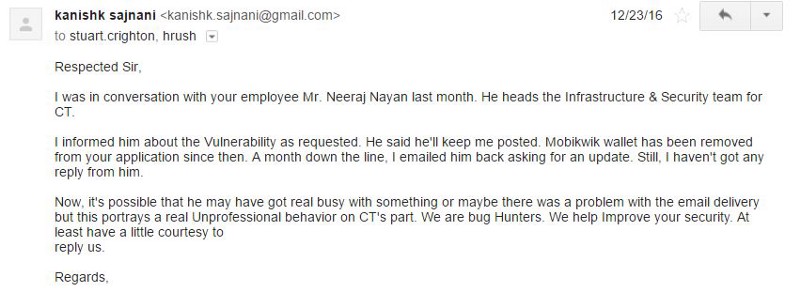
Now, the least they could’ve offered me was a proper acknowledgement. Could have shown a little gratitude. I was not the one to ask for a reward. What a shame! What I’ve learnt from my experiences? 1) Indian companies don’t pay attention required for security of their products. 2) No Application/Website is entirely secure. Chances are, maybe someone is already exploiting the bugs right under their nose. 3) The only way they understand the importance of Bug Bounty programmes is through public humiliation. Damage control is obligatory once you get hacked. Best Example - Ola Cabs. 4) Ethical Hacking is rarely appreciated. 5) The process of Resolution usually takes a lot of time here. I remember submitting a vulnerability to Mobikwik through their Official Programme. I was just able to brute force the OTP during Account Creation. They took like five weeks to get it over with & rewarded me with a sum of Rs 2,000. What needs to be changed? Everything. From cyber laws to the way security is dealt in our country. 1) Development & Maintenance isn’t everything. The company should be secure from any kind of hacking attempts. Leak of private customer details would mean a massive lawsuit coming your way. 2) Every big startup/company should opt for a Bug Bounty programme Or at least have a responsible disclosure policy. Platforms such as Hackerone Or Bugcrowd can be used too. 3) Appreciate & acknowledge those who find loopholes in your system. 4) The Cycle of Bug Identification- Resolution- Reward should be as fast as possible. 5) Companies that don’t have their own security Engineers can hire other firms to test their API’s.
My Story I was inspired to start learning about Internet security around June 2015. A story about how someone hacked into something & got rewarded for the same would pop-up regularly. I thought I could use these additional skills to my advantage too (being a computer engineer in the making). I started out on my own (bit by bit) learning things from the Internet. No books to refer or teachers to learn such stuff from. I would download the required tools/software & start experimenting. Initially, it was bit scary. I was afraid that this hit & trial method may cause me legal trouble. Eventually, I was able to understand everything. I found my first ever vulnerability in Faasos application. It was a jackpot. I was able to lookup the details(Debit card, Addresses, Order History) of any customer just through their email address or Mobile number. Furthermore, I was even able to Order anything for free. I literally owned the application thereafter.
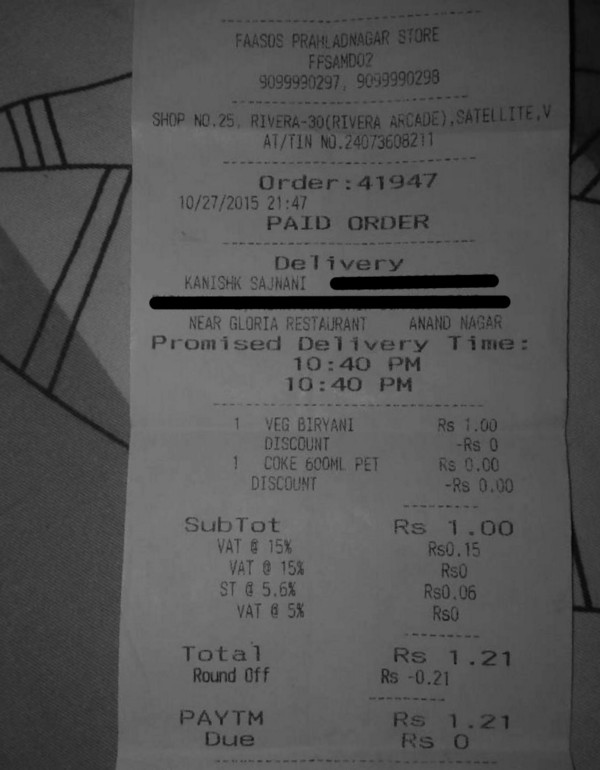
Full disclosure? I did order a Free Biryani couple of times 😆What surprised me was the fact that no-one from the store manager to delivery boy realised that they were being duped. The first time, I paid in cash after explaining them everything. The second time was a test & they failed again. I could’ve eaten more like a 1000 times. Soon after, I found out the email address of their CEO Mr. Jaydeep Barman & mailed him. I even exchanged a few emails & calls with his brother(also CTO). As it usually happens, the vulnerabilities remained unpatched for almost six months until they hired a security firm ‘Falliable’. I now find a unique interest in doing what I do. Some people may find this a bit boring, but for me, it’s like treasure hunt — Exploring & finding out stuff that’s never seen before. It’s time for me to further polish my hacking skills. Looking forward to join some professional courses.
This post first appeared on Medium. Republished with permission. This post has been edited for brevity. Disclaimer: BOOM has not been able to independently verify all the claims made by the author in the story.